Quantum Risk: Closer Than You Think?
\ “Quantum Day is coming - are you ready?” The question gets asked often. The answers usually assume long timelines and orderly transitions. Emerging signals, including AI-accelerated research, suggest that such assumptions may be fragile. We could be closer than expected. This article shares several factors that support that perspective.
January 1, 2027
The NSA has a line in the sand. As of 2027, the vast majority of newly acquired NSA systems must be compliant with post-quantum cryptography (PQC). The requirement was published in April 2025 in the CSfC Post Quantum Cryptography Guidance Addendum 1.0. \n \n NSA timelines usually lead institutional adoption by a few years. In the case of quantum computing, that precedent isn’t particularly comforting. Today’s technological and geopolitical conditions introduce risks, some of which lack historical analogues, and timelines could shift with little or no warning.
AI + Quantum = Acceleration
Advances in AI are feeding back into quantum research at an increasing pace. Improvements in neural network design, reinforcement learning, and optimization techniques are being applied to practical problems like qubit control, calibration, error correction, and hardware layout. The result is a development curve that can compound, allowing progress to stack faster than the familiar step-wise path from theory to working systems. The feedback loop is already visible in literature.
Sources: National Science Review (2025), Nature Communications (2025), and Physical Review X (2022).
This small sample is also enough to suggest that quantum progress can transpire unevenly, and in capability-specific bursts.
What You Don’t See is What Should Concern You
University labs and many corporate research programs frequently demonstrate their love for announcing milestones. That said, nation-states and the private sector are really under no obligation to do so, and in some cases they don’t. Governments have been known to quietly absorb private efforts and classify progress, and strategic players may deliberately choose stealth over publicity. There are often real advantages - such as the option to deploy quietly while competitors, adversaries, or potential targets, operate under false assumptions and fail to react in time.
History gives precedent: from Bletchley Park’s WWII cryptanalysis, through Cold War efforts like Operation Ivy Bells, to modern cyber operations like Stuxnet, powerful capabilities have frequently been deployed quietly long before public disclosure.
Quite a few organizations are currently racing to build large-scale facilities for AI training and inference. These environments of dense compute, specialized cooling, and restricted access overlap in important ways with the infrastructure required for advanced quantum-computing research. As a result, the rapid expansion of AI-focused facilities adds signal noise, making it harder to infer the pace or scale of parallel developments elsewhere.
The Economics of HNDL (Harvest-Now, Decrypt-Later)
In 2022, the WEF published a white paper titled “Transitioning to a Secure Quantum Economy”, co-authored with Deloitte. It asserts that harvest-now, decrypt-later (HNDL) risks—particularly for data with long exposure—require organizations to act early by building awareness, educating leadership, and developing migration roadmaps toward quantum-safe strategies.
I’ll be explicit. A well-funded organization does not need universal, faultless, economy-of-scale quantum to compromise widely used cryptography. They only need sufficient density and efficiency to push infrastructure, bootstrapping, and operational costs into a range where brute-force investment becomes viable.
Unlike many commercial systems, Bitcoin in particular faces adversaries whose motivations may not be stymied by typical economics. Strategic, political, or ideological considerations can justify investments that would otherwise appear uneconomical under standard models.
Background: Readers who want to know more about the Bitcoin community’s current response to the challenge of quantum will find BIP-360: Bitcoin’s Quantum Wild West interesting.
For adversaries already in possession of encrypted datasets, the strategy is straightforward: store now, decrypt later. At some point, the economic balance shifts, and when it does, years (or decades) of sensitive data become exploitable.
The risk becomes more apparent when you consider that exploitation isn’t binary. It could unfold on a spectrum, ranging from subtle activity that flies under the radar like selectively targeted exposed signatures misattributable to poor key management or even seen as a normal activity, to bold events that disrupt whole industries and upend established security norms.
Global Warnings Issued
Organizations like the World Economic Forum (WEF) have warned of the possibility of a large-scale cyber event with impacts exceeding COVID-19. Based on the results of their tabletop exercises and follow-on analyses, society remains poorly prepared for systemic cyber shocks.
Quantum-enabled cryptographic compromise is a credible candidate for such a disruption, and it doesn't necessarily depend on universal quantum capability. The WEF’s planning should be read as a signal to prepare for a form of discontinuity that existing cyber risk models don’t fully capture.
Don’t Be Surprised When Dates Move
NIST and other standards bodies are deliberately cautious and responsible, trying to signal appropriate urgency while avoiding panic or premature commitment. They will be left with very little wiggle-room if events accelerate unexpectedly, when compressed timelines will start resulting in fragile implementations.
The Bottom Line
Yes, Quantum Day is coming. It’s likely to arrive sooner, under more opaque circumstances, and with higher stakes than most organizations expect. Waiting for public announcements is a dangerous strategy.
Those who adapt beforehand will be in a better position.
Support the Author
BTC: bc1qsmlpjg8n24m4ufnvd2tsgutuc0cpy4a04jrwml
\n \n \n \n
\n
\
You May Also Like
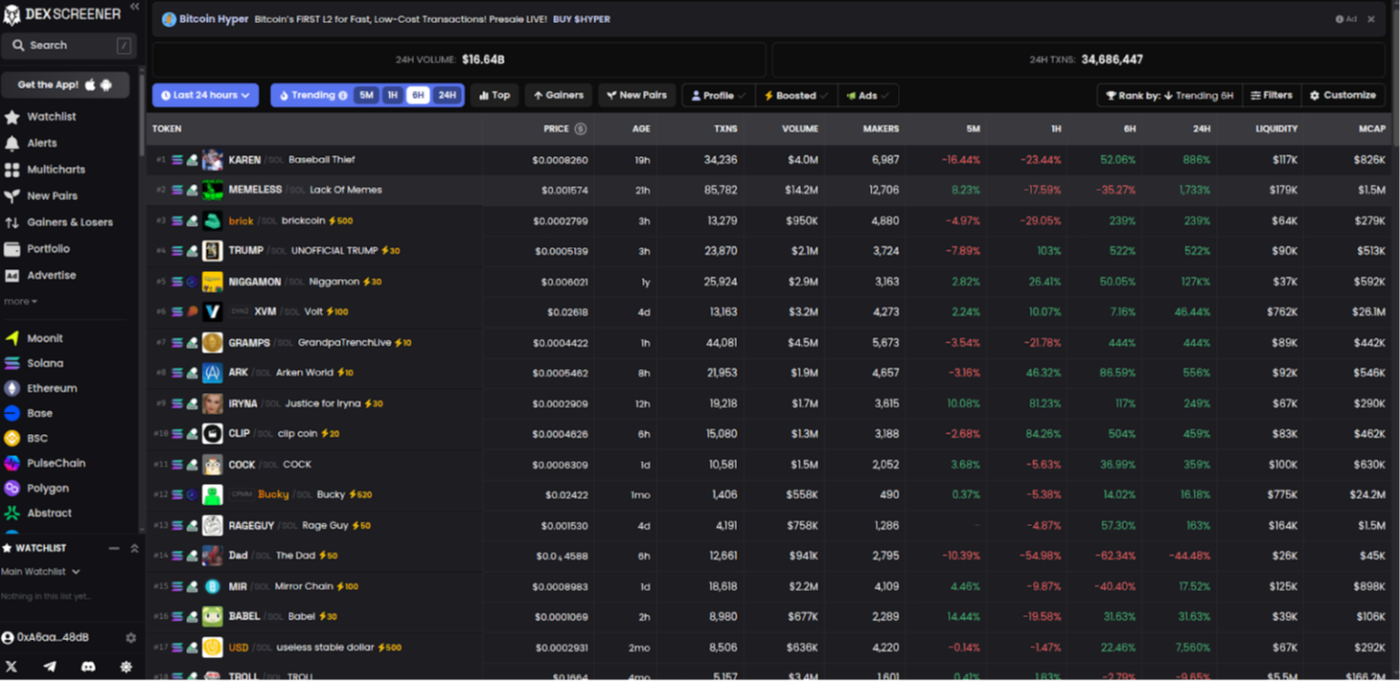
Building a DEXScreener Clone: A Step-by-Step Guide
Which DOGE? Musk's Cryptic Post Explodes Confusion
